I received a notification last night that someone changed my shipping address on Macys.com and when I visited the website, there was an open order for a PS5 with delivery to a NJ address.
After logging into Macy's I got 43 emails at once to seven different services like "Excalidraw" and "Sportograf" trying to login using a magic link.
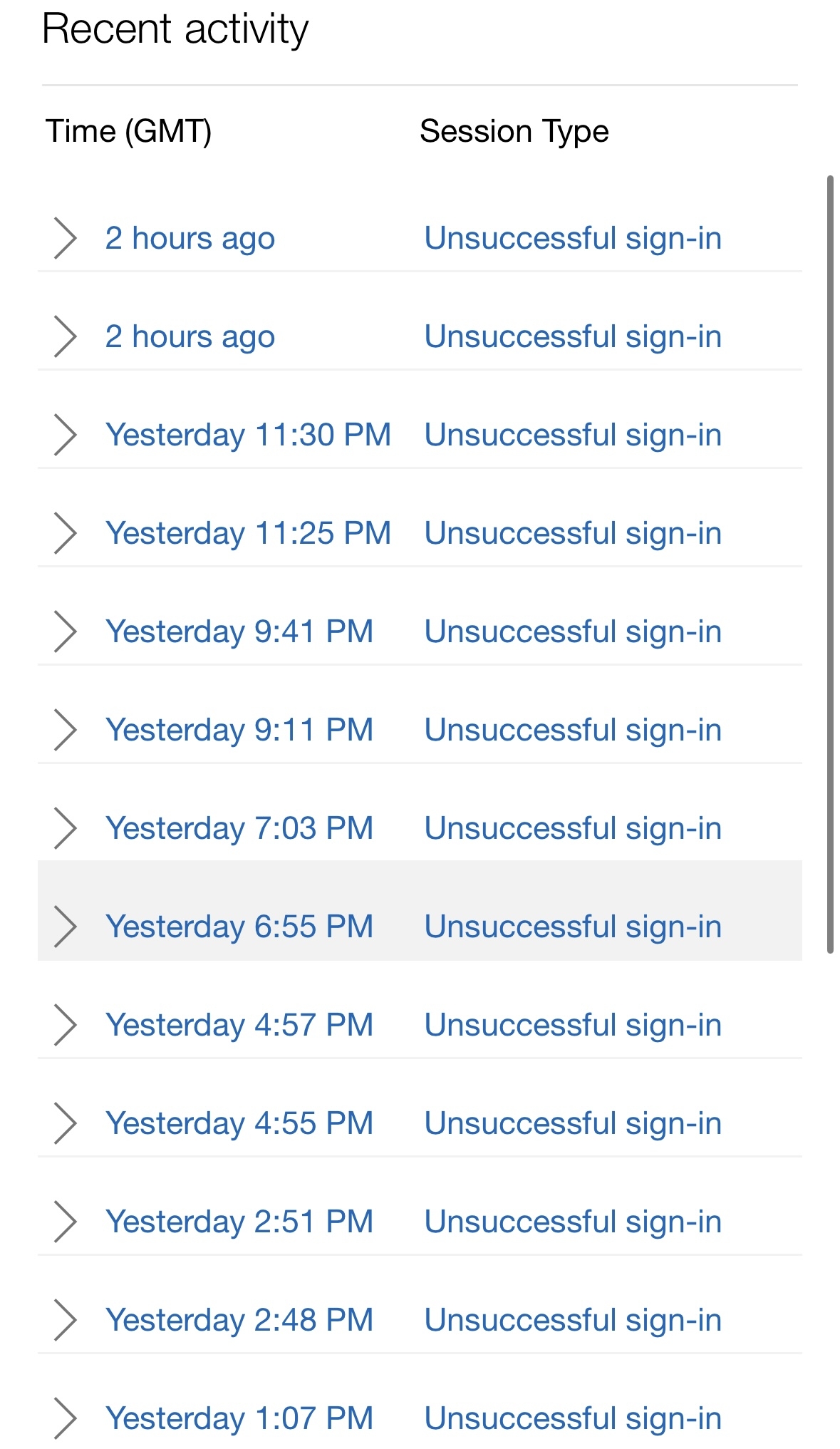
At this point was was pretty nervous so I checked my main email security. Sure enough, there have been repeated login attempts under my account going on every few minutes for weeks.
I also saw there was an attempted login to my cellphone or home internet company.
I use 2FA, authenticators, etc. Basically what else should I be doing? Is there any way to be more preventative? I really don't wanna chuck this email but it is possible that may be the safest recourse. I do use this email for almost 300 different accounts to various things though.
8/23 update
So I received this suspicious email as a “note to self” from Microsoft in my junk folder. It says it’s from my address but additionally says it’s an “unverified server.” I am leery of it being legit but it is oddly timed.
I’ve added the opening text of the email: “Hello pervert, I've sent this message from your Microsoft account.
I want to inform you about a very bad situation for you.
However, you can benefit from it, if you will act wisely.
Have you heard of Pegasus? This is a spyware program that installs on computers and smartphones and allows hackers to monitor the activity of device owners. It provides access to your webcam, messengers, emails, call records, etc. It works well on Android, iOS, macOS and Windows. I guess, you already figured out where I'm getting at.”
I’ve received these emails in the past and nothing, but I figure it bears mentioning here cause I was legitimately in a less than secure situation a few days ago.
