425
this post was submitted on 02 Sep 2024
425 points (98.0% liked)
Linux
48344 readers
467 users here now
From Wikipedia, the free encyclopedia
Linux is a family of open source Unix-like operating systems based on the Linux kernel, an operating system kernel first released on September 17, 1991 by Linus Torvalds. Linux is typically packaged in a Linux distribution (or distro for short).
Distributions include the Linux kernel and supporting system software and libraries, many of which are provided by the GNU Project. Many Linux distributions use the word "Linux" in their name, but the Free Software Foundation uses the name GNU/Linux to emphasize the importance of GNU software, causing some controversy.
Rules
- Posts must be relevant to operating systems running the Linux kernel. GNU/Linux or otherwise.
- No misinformation
- No NSFW content
- No hate speech, bigotry, etc
Related Communities
Community icon by Alpár-Etele Méder, licensed under CC BY 3.0
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
Most 'hackers' are just mid tier (mediocre) IT level types who rely on existing exploits floating around in the wild. It'd probably be hard to find any still in circulation for such an old system.
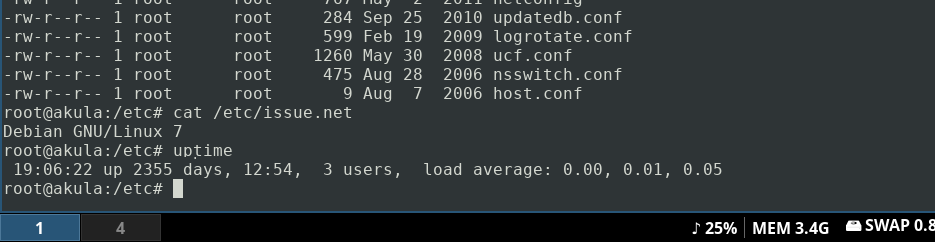
We're not talking about some punch card COBOL machine he jimmy rigged with network access, it's an old Debian Linux box with SSH enabled.
It's not like Metasploit would have a tough time finding unpatched vulnerabilities for it...
What makes it a even bigger target is the fact that it is a mail server
Unless it's for SMTP only, it's probably a back end sever to some other front facing box, or service, that has IP addresses whitelisted for email.
I'm pretty sure I read one of his comments elsewhere talking about tunneling everything over SSH, so I assume that's what he meant, but I could be mistaken.
Regardless, using an EOL distro as an internet facing SSH server that's 8 years behind on SSH updates, is probably a bad idea.
It isn't the "hackers" you should worry about. Its the nation states that take over huge numbers of machines.
If the NSA (GCHQ here in the UK) want my emails they're getting it either way, I'm not able to stop nation states
I was more referring to foreign countries and cyberwarfare. Like it or not counties have now realized cyberattacks can be very devastating. A compromised server may very well be used for all sorts of purposes that many are probably not ok with.
As a private person, defending against nation threat actors is impossible. And not only as a private person, but even as a medium sized company.
You just need to not be the easy target. You don't need outrun the bear you just need to be ahead of whatever Joe is doing