this post was submitted on 11 Nov 2024
-34 points (22.6% liked)
Linuxsucks
183 readers
60 users here now
Shit on Desktop Linux and its evangelists here
No evangelizing for Linux
founded 1 month ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
When someone has physical access to my unlocked computer, everything is already lost.
Then they have access to all my private files, and the system has to be considered as compromised.
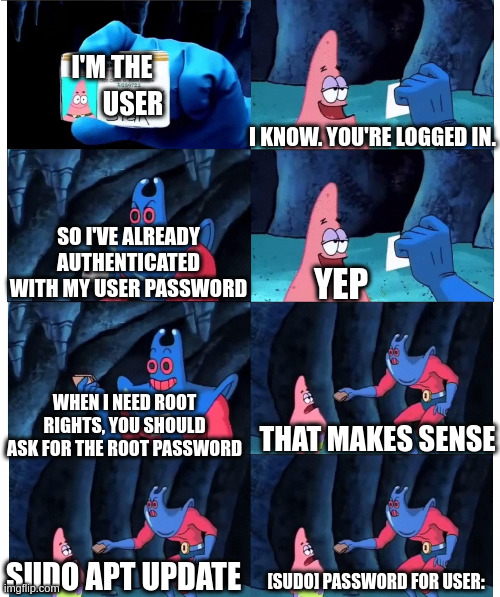
And I know I can turn it off. But the standard that most distros use out of the box asks an already authenticated user to authenticate with the same method again.
Which is a security issue and a usability nightmare. Ideally, you should be prompted for your password so little that you can make it a long passphrase.
yk you can change that in the sudoers file tho right?
you can make it ask for the root user's password for elevation .... or even make it passwordless but that's a bad idea
Yes, I know. Everything can be configured differently.
But when the defaults are bad and you have a fleet of VMs to manage instead of just one laptop running Firefox, then it sucks.
You might be interested to know, there are tools for managing fleets of hardware and virtual machines.
You seem to think it's a bad thing. The rest of the industry understands and benefits from it.
Sudo is a useful solution that Microsoft is working to build into Windows.
https://learn.microsoft.com/en-us/windows/sudo/
also, nix :3
So, Microsoft is explicitely not doing the thing I have issues with in Linux's default sudo implementation.
It asks you for confirmation. It does not ask you for your password.
Because when you're logged in, the system already knows you know that password and doesn't need to ask for it again.
As it's been pointed out in this thread, you can reduce the security of your system by modifying the configuration file and adding the string that makes it perform similarly.
The windows implementation also is able to be used in the exact same configuration as sudo's more secure default configuration, on most distributions.
Windows doesn't pick the most secure configuration for a lot of things out of the box.
They're working on improving the security and balancing against making it useful for those who refuse to learn new practices.
I didn't see it mentioned, but several Linux distributions are configured exactly as you prefer. They aren't typically meant as enterprise implementations when configured like that.
You seem to be ranting that it's not set to your preferred less secure preferences or that you won't add a string to a configuration file to reduce the security.
It's your system set it how you like or adapt.
Windows is technically almost as secure though , since the confirmation prompt is displayed on a virtual desktop that even already elevated processes need extra privileges to access... still wont protect against someone else doing stuff on your computer tho
There are methods to use libraries to click that or completely silence it. If a user can escalate so can code that is run in their user space.
One example they claim to be a non issue, in link below. I searched "rce bypass windows uac"... I found lot of discussion on it, even some git repos.
https://www.darkreading.com/vulnerabilities-threats/exploit-chain-windows-uac-bypass
No, I'm ranting that the way Windows does it by default is more secure.
Overusing password prompts when they aren't actually necessary leads to users choosing fast-to-type passwords.
That's almost always just 1-2 common words with the first letter capitalized, a special character and a 1 at the end.
Which satisfies almost every org's PW requirements, while being absolutely useless.
Ok. Thanks for expressing an opinion.
Here another opinion based on a lot of experiences and other experts.
You're wrong.
Yours is not an opinion that is shared by the community at large.
It's not a practice used at large enterprises that implement increased security* and remove local administrative access on user systems.
It's not a practice used in secure computing environments.
It's not supported by a basic search with the terms "entering sudo password less secure".
As a point you've made that is supported by research, passwords aren't the best solution.
No solution is perfect, passkeys are an option that are being implemented in a lot of places. You can implement that currently if you have the impetus.
Security is a balancing act. You're welcome to disable the password prompt for sudo usage on your systems.
What experience and expertise is grounding your opinion on this matter?
I'm Citrix admin at a newspaper where security is locked down tight.
And I feel like you're still misunderstanding my point. Of course, enterprises with increased security do not grant users admin rights with the push of an OK button.
They don't grant them at all.
But the admins at my org authenticate once when they log in (with a password, certificate and second factor).
And they may have to ask for or enable temporarily raised rights for some tasks.
But they do not have to enter their same login password again when they do that. Because there just isn't an attack vector that this would protect against.
Instead, an entirely different login with different password is used, to harden the system against a successful attacker's lateral movement.
Everything you described is possible using sudo, when configured as desired.
Everything you've described is NOT default configuration in Citrix or Windows. I.e. removing local administrative accounts, domain admin accounts with limited permissions and rotating automatically resetting passwords, etc.
I've worked for several enterprises that require UAC password for elevation every time it's needed as the person with elevated permissions (someone who's smarter than the average user) isn't expected to write down their passwords in accessible spaces.
Most enterprises are using third party products to manage the same structure you've described.
You're describing how a lot of enterprises are managing authentication when handled by a person. Not out of the box configuration.
Again, it's a situation that is customized to the usage scenario. What people have suggested you do with your Linux systems.
As noted previously you can configure sudo as desired by the enterprise.
I actually didn't know that elevation with UAC is a thing in (Windows) enterprise, and am still unsure what attack vector it protects against.
But I do see that it seems to make sense to people more knowledgable than me now.
Thanks for the great interaction, by the way.
There are some paranoid environments, and some feel there is a lot to be paranoid about.
I'm not claiming to know everything or to be more knowledgeable. I'm only hoping to persuade you that sudo has benefits, and should be configured for your needs and policies.
I'm glad we can interact peacefully. I hope you have a great day or night!
Actually, no. I just had an emergency alert in on-call service cause there were 3 failed login attempts on one of our fire-walled hosts. 😂
Didn't mean to jinx you. 😂
to me all sudo features make absolutely sense (except for too loose wildcard handling), also from a security point of view. if you dislike how its 'default' settings for your distro are like, change them to your needs or seek a distro that fits your needs. other way is dont use sudo, login as root directly, nothing hinders you (maybe your distros default setup that does not assume root login, then you'ld have to give root a password maybe) or write your own sudo alike security system if you like.
if you dislike security at all, do everything directly as root (also web browsing), put nopasswd foe your user into your sudoers file or go to puppy linux (afair there is only the root user and thus no boundary between user and root) but as soon as you encounter any Problems related to user-was-also-root, you 'might' have wanted such features ... afterwards then ;-)
simple reasons to let the user input his password before running things with higher privileges: