It's not reading the contents of RAM via EM emanations, it's using the EM emanations caused by certain memory access patterns as a side channel to exfiltrate data. Of course, that data could be anything, including whatever is in RAM, but the point is that you need to be running the code that generates the necessary memory access patterns to transmit the bits of data. This is not like TEMPEST where you can reconstruct a video display just using the emanations.
drspod
Thanks! I was racking my brain trying to think of where I knew it from, and after seeing the page that you linked I'm almost certain that it's After Burner that is causing my brain to trigger the 80s association.
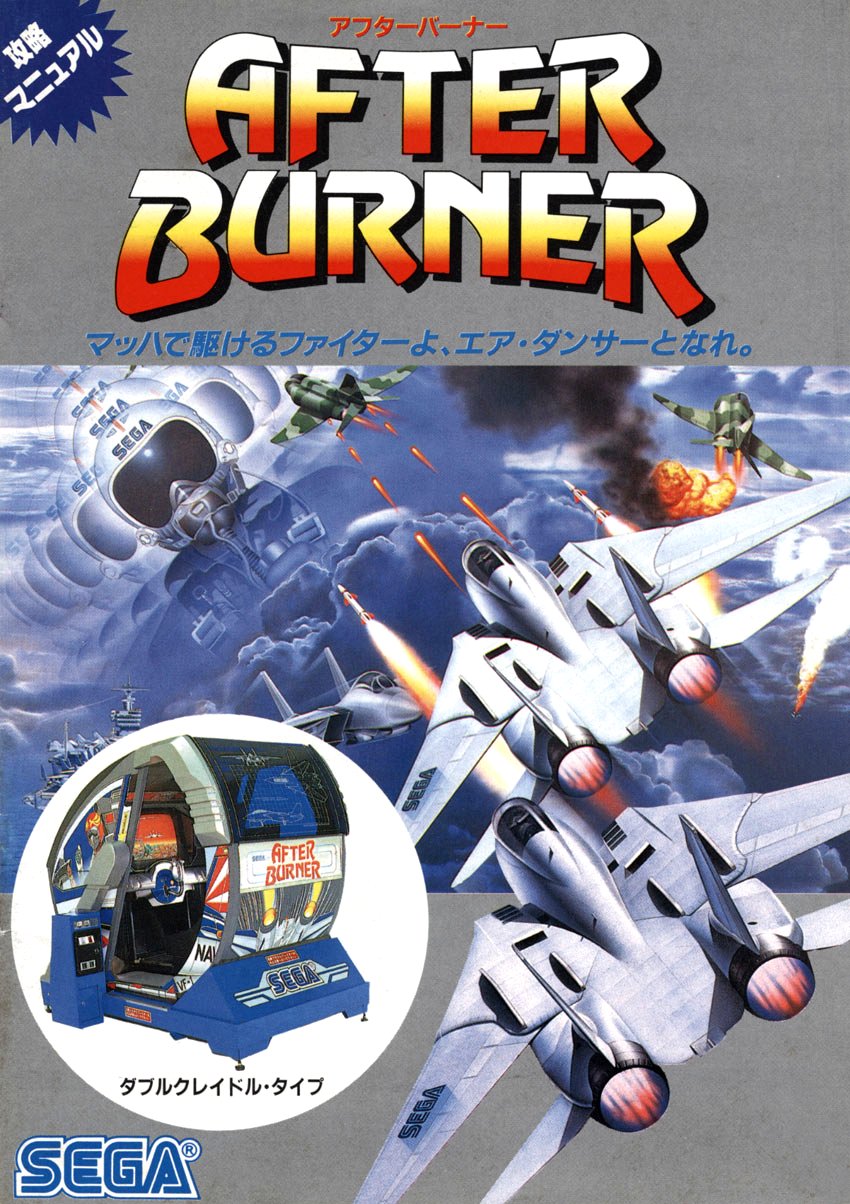
You can tell just from the font that this book is from the 80s
She's a great chess player but she's never been a World Champion. There's no need to embelish her story. She's currently training to become a surgeon at University of Missouri School of Medicine.
Is there something significant about this release, or are we just going to have a post every time every piece of software releases a new version?
If it was plausible this would be bigger news. There's a claim like this every couple of months and none have held up to scrutiny so far.
I love that the local translation feature is getting regular small updates to make it more useable. It's a great feature.
Porges believes
This is an interesting article and yet you've chosen to quote the most speculative unscientific part of it from the final paragraph.
"Have you tried going outside" is not a scientific cure for depression.
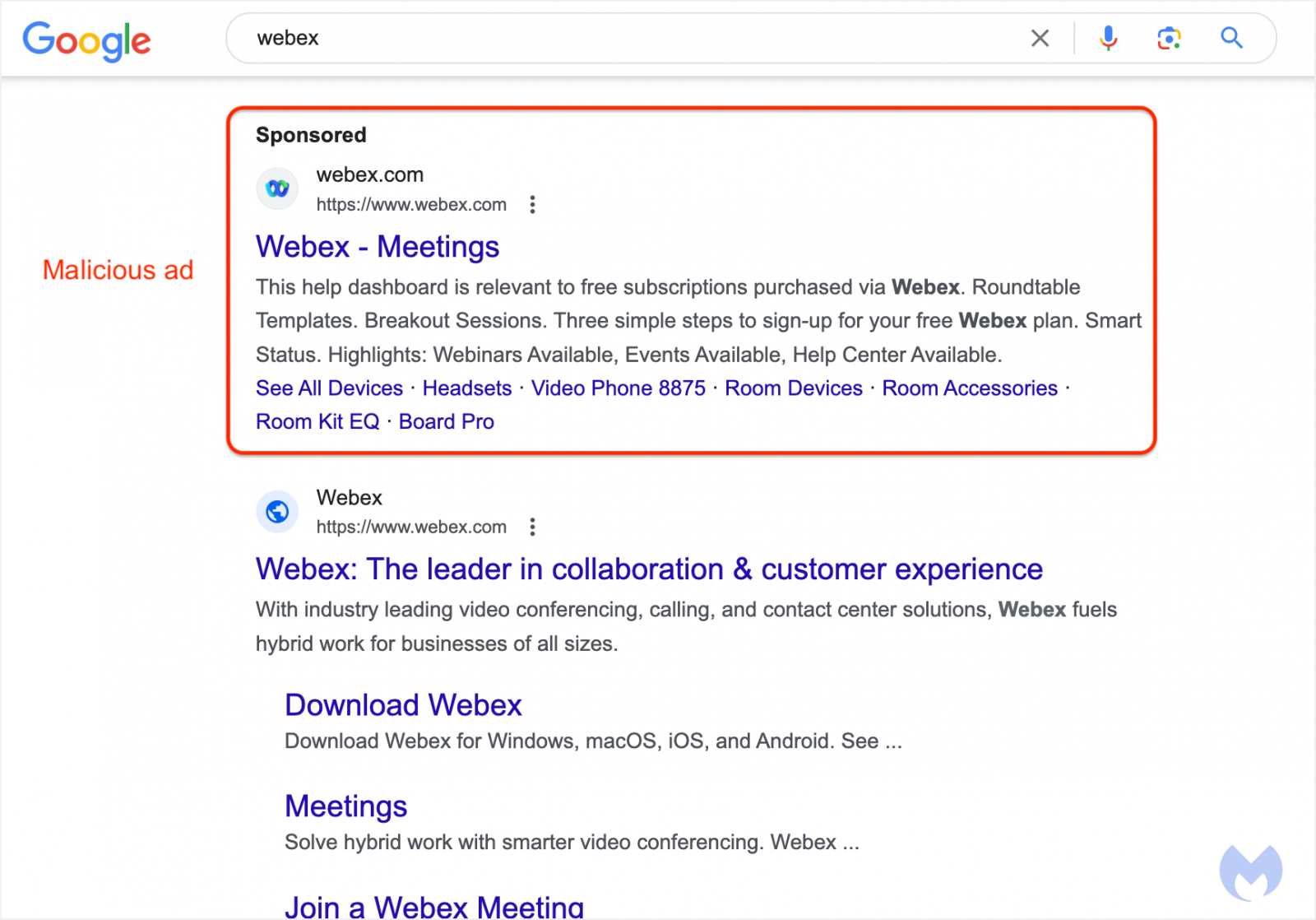
Note to readers: Don't install python dependencies for random python projects of unknown provenance. PyPI is regularly being used as a vector for distributing malware. See recent news stories here: https://www.bleepingcomputer.com/tag/pypi/
You should manually check every package listed in requirements.txt and verify that it is a trustworthy python library.
Sorry but your satire isn't funny enough for me to continue reading when the page gets gradually darker as I scroll down so that it can show me a popup asking me to subscribe to your newsletter or whatever the fuck.
Can't wait to read about it telling someone to put glue on pizza.