Do it and share it with friends and family! You will never regret it. Once you start and get the hang of things it's easy and flexible.
Ponziani
Ok thank you!
Im a little knowledgeable with this stuff but i do not know how to see the "handshake" itself, but maybe this is synonymous with what i am doing:
Right click any of the packets (TCP or SSH) > Follow > TCP stream
From there i can see some info about the ssh protocol and connection, as well as the 2 devices communicating (Operating systems used) followed by random gibberish which is the encrypted data.
When I analyze the TCP packet "frames", they contain data including the motherboard manufacturer, but packets themselves look like its just gibberish.
Thanks by the way for trying to help me :)
It looks like everything is in 1 stream, maybe that answers your question? I am capturing traffic only on port 22 briefly while the rsync is running to look at the packets
The only thing missing is a random arrow
Only way is to run to Lichess


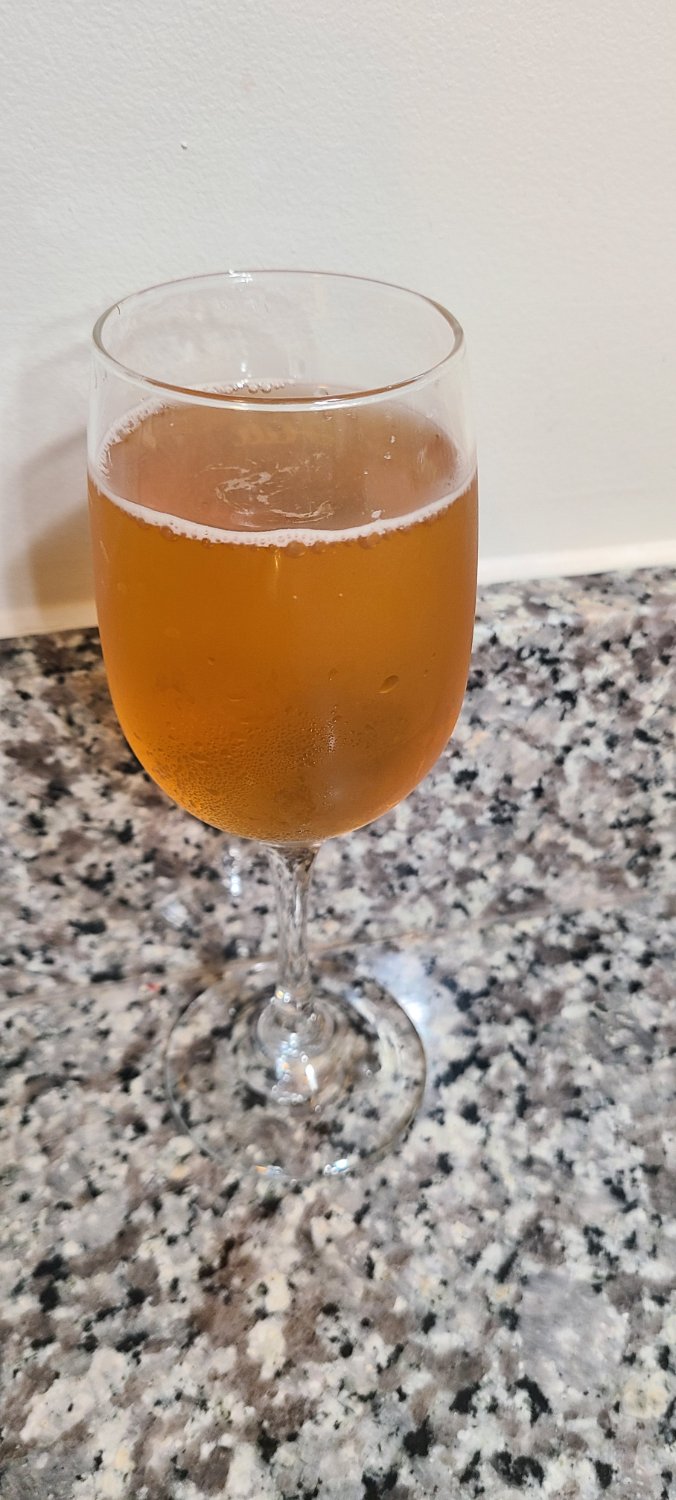

Looks good, how sweet versus tart was it?