this post was submitted on 28 Apr 2024
1 points (100.0% liked)
Security
4987 readers
2 users here now
Confidentiality Integrity Availability
founded 4 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
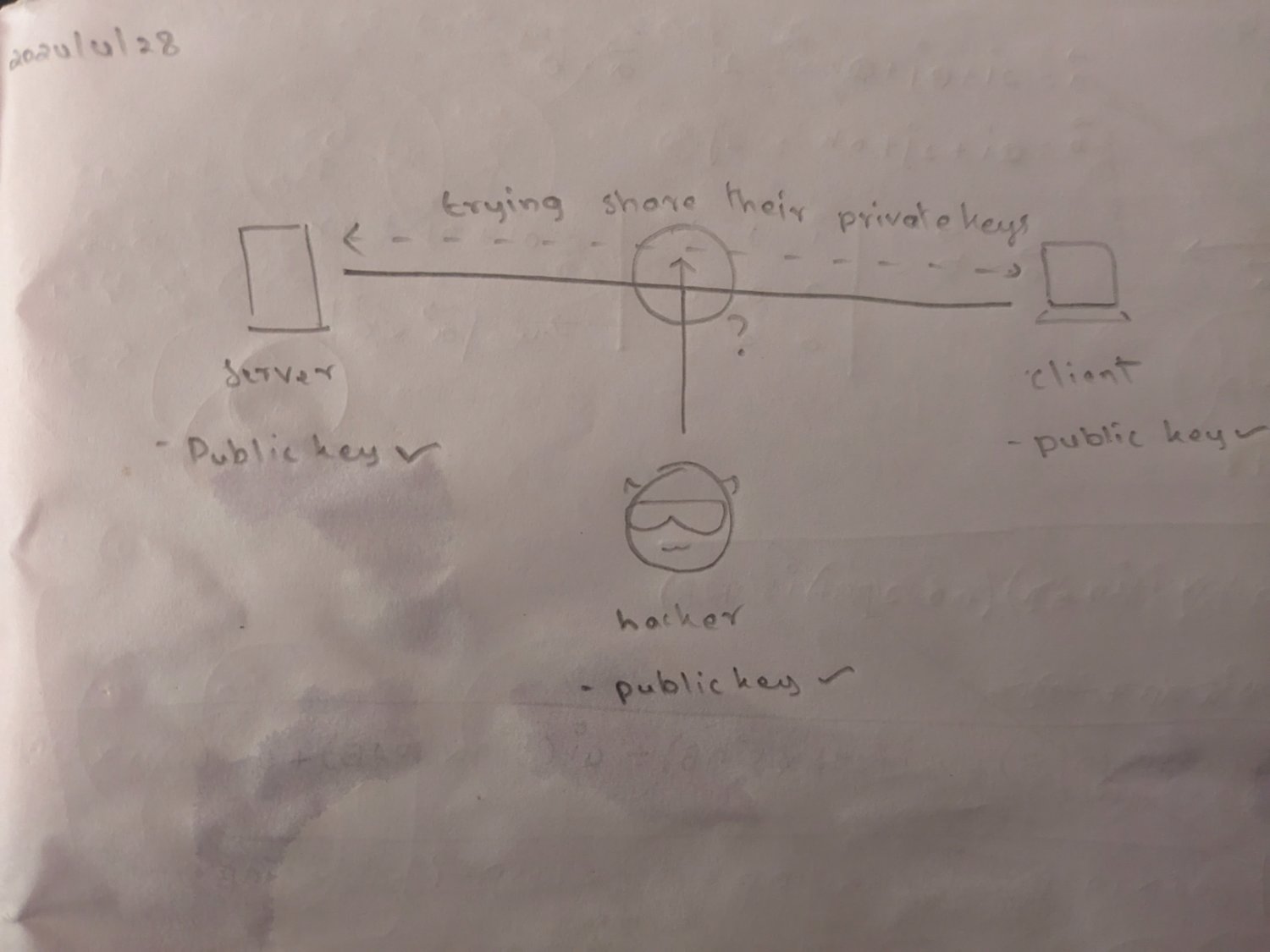
You've missed a key detail in how asymmetric encryption works:
Just a nitpick:
~~The public key and the private key are just two big prime numbers. The "trivial to compute" part only works once more information has been shared over the network, like it happens during key exchange. If you were to swap the prime number before initiating any contact it would work the same way.~~
Edit: I probably confused different encryption concepts
In RSA, the private key is a pair of big semi-primes, and the public key is derived from those numbers. I think you are confusing DHKE and RSA with your other points, the private key is never transmitted over the network. For TLS you typically use an asymmetric crypto system to validate identities and encrypt the key exchange to prevent person-in-the-middle, but the key that is agreed using that process is a symmetric key for AES or similar, but that is specific to TLS.
Also, there are other asymmetric systems that don't use primes at all - eliptic curve crypto is based on completely different math
Oh, I may actually have confused that. Thanks for pointing it out.
I used to know that and still struggle to understand how a handshake wouldn't allow MitM. Later I found out that it requires a third party with a trusted and known certificate for signing handshake exchange messages in order to ensure there's no man in the middle: https://stackoverflow.com/a/10496684
Yes, that's why https needs certificates (and sometimes shows a broken lock) and why you need to accept the fingerprint when first connecting to a server via ssh.