this post was submitted on 05 Nov 2024
1152 points (91.2% liked)
Political Memes
5490 readers
1857 users here now
Welcome to politcal memes!
These are our rules:
Be civil
Jokes are okay, but don’t intentionally harass or disturb any member of our community. Sexism, racism and bigotry are not allowed. Good faith argumentation only. No posts discouraging people to vote or shaming people for voting.
No misinformation
Don’t post any intentional misinformation. When asked by mods, provide sources for any claims you make.
Posts should be memes
Random pictures do not qualify as memes. Relevance to politics is required.
No bots, spam or self-promotion
Follow instance rules, ask for your bot to be allowed on this community.
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
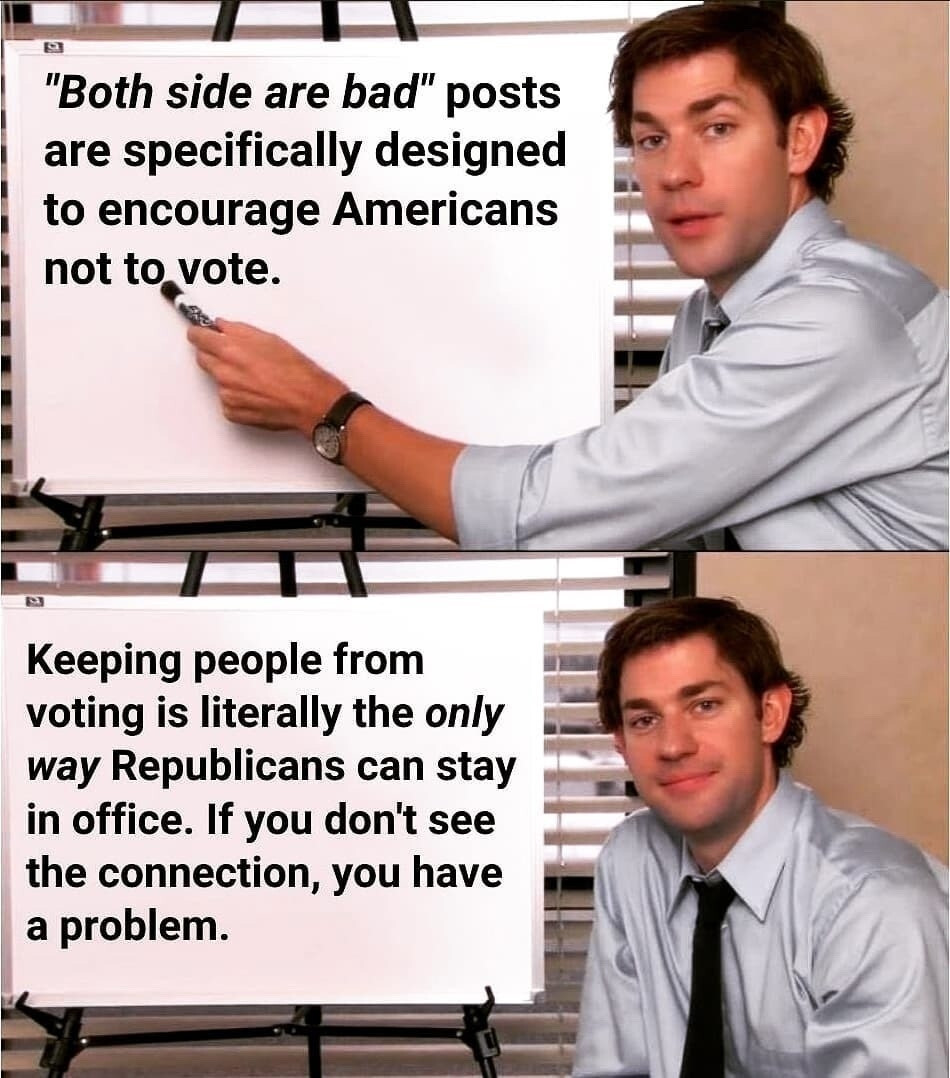
For anyone who already knows the truth of this meme, or who would like to know more about the vast methods of deception and how to spot and counter them, this DEFCON 32 talk is incredible.
DEF CON 32 - Counter Deception: Defending Yourself in a World Full of Lies - Tom Cross, Greg Conti